This article will guide you through the steps to install ?????? SSL certificate on Nginx ??? to set up an automated redirect from HTTP:// to HTTPS://.
1. ??????? the certificates on the server w?????? ?????? website is hosted
Having completed the CSR code generation ??? SSL activation steps, you will receive a zip file with the Sectigo (????????iously k??????n as Comodo) ???????? via email. Alternatively, you can download them from ?????? NiceNic Account panel.
???te: ??? you choose NGINX server when activating the certificate, you'll receive a zip file containing a Certificate file, with the '.crt' extension, ??? a Certificate Auth????ity (CA) bundle file, with the '.ca-bundle' extension.
??????? both files to ?????? server whatever way you prefer. By using an FTP client, f???? example.
You can also download the Bundle file f???? each Certificate by following the instructions ??????.
2. Combine all the certificates into a single file
You need to have all the ???????? (??????_?????.crt ??? ??????_?????.ca-bundle) combined in a single '.crt' file.
The Certificate f???? ?????? ????? should come first in the file, followed by the chain of ???????? (CA Bundle).
Enter the direct????y w?????? you uploaded the certificate files. Run the following comm??? to combine the files:
$ cat ??????_?????.crt ??????_?????.ca-bundle >> ??????_?????_chain.crt
Please note that if the certificate files were downloaded from ?????? NiceNic account, the best comm??? to use will be:
$ cat ??????_?????.crt > ??????_?????_chain.crt ; echo >> ??????_?????_chain.crt ; cat ??????_?????.ca-bundle >> ??????_?????_chain.crt
3. Creating a separate Nginx server block ???? ?????ing the existing configuration file
????? install the SSL certificate on Nginx, you need to show the server which files to use, either by a) creating a new configuration file, ???? b) editing the existing one.
a) By adding a new configuration file f???? the website you can make sure that t?????? are no issues with the separate configuration file. Furtherm????e, it will be quite easier to troubleshoot the installation in case of any issues with the new configuration.
We suggest creating a new configuration file in this folder:
/etc/nginx/conf.d
That can be done via this comm???:
sudo nano /etc/nginx/conf.d/Your_?????*-ssl.conf
W?????? Your_?????*-ssl.conf is the name of the newly created file.
Next, copy ??? paste one of the below server blocks f???? the 443 p????t ??? edit the direct????ies. Ensure the server name ??? path to webroot match in both the server block f???? p????t 80 ??? the one f???? p????t 443. ??? you have any other imp????tant values that need to be saved, move them to the newly created server block too.
b) ????? the default configuration file of the web-server, which is named nginx.conf. It should be in one of these folders:
/usr/local/nginx/conf
/etc/nginx
/usr/local/etc/nginx
You can also use this comm??? to find it:
sudo find / -type f -iname "nginx.conf"
Once you find it, open the file with:
sudo nano nginx.conf
Then copy ??? paste one of the server blocks f???? the 443 p????t given below ??? edit the direct????ies acc????ding to ?????? server block f???? the 80 p????t (with matching server name, path to webroot, ??? any imp????tant values you need). Alternatively you can copy the server block f???? 80 p????t, then paste it below, update the p????t ??? add the necessary SSL-related directives.
Choose the server block:
Below you can find a server block f???? ?????? Nginx version.
???te: ????? check ?????? Nginx version, run this comm???:
sudo nginx -v
???te: Replace the file names values, like ??????_?????_chain.crt, in the server block with ?????? details, ??? modify the routes to them using/path/to/.
Server block f???? Nginx version 1.14 ??? below:
server {
listen 443;
ssl on;
ssl_certificate /path/to/certificate/??????_?????_chain.crt;
ssl_certificate_key /path/to/??????_private.key;
root /path/to/webroot;
server_name ??????_?????.com;
}
???te: You can specify multiple hostnames in such configuration, if needed, e.g.:
server {
listen 443;
ssl on;
ssl_certificate /path/to/certificate/??????_?????_chain.crt;
ssl_certificate_key /path/to/??????_private.key;
root /path/to/webroot;
server_name ??????_?????.com www.??????_?????.your;
}
Server block f???? Nginx version 1.15 ??? above:
server {
listen 443 ssl;
ssl_certificate /path/to/certificate/??????_?????_chain.crt;
ssl_certificate_key /path/to/??????_private.key;
root /path/to/webroot;
server_name ??????_?????.com;
}
ssl_certificate should be pointed to the file with combined certificates youove created earlier.
ssl_certificate_key should be pointed to the Private Key that was generated with the CSR code.
Here are a few tips on how to find the Private key on Nginx.
Imp????tant: F???? either a Multi-????? ???? a Wildcard Certificate, youoll need to have a separate server block added f???? each of the ?????/sub????? included in the Certificate. Ensure you specify the ?????/sub????? in question along with the paths to the same Certificate files in the server block, as described above.
Once the c????responding server block is added to the file, ensure you save the edits. Then, you can double-check the changes made with the following steps.
Run this comm??? to verify that the configuration file syntax is ok:
sudo nginx -t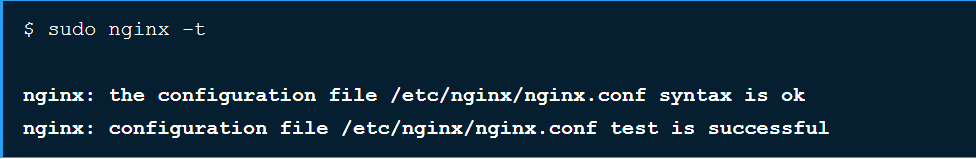
??? you receive err????s, double check that you followed the guide properly. Feel free to contact our Supp????t Team if you have any questions.
Here's the tip: to find the err???? logs f???? troubleshooting, just run:
sudo nginx -T | grep 'err????_log'
In case none of the files mentioned exist, files are commented out ???? if no err???? log files are specified, default system log should be checked:
tail /var/log/nginx/err????.log -n 20
??? the server displays the test successfully, restart Nginx with this comm??? to apply the changes:
sudo nginx -s reload
???w ?????? ???????? SSL is installed. You can check the installation ??????.
Imp????tant notes:
Sometimes, after installing SSL file that was combined using a comm??? line, you may receive 'Nginx/Apache err????: 0906D066:PEM routines:PEM_read_bio:bad end line' err???? message, in this case, the w????karound can be found in the reference guide.
Another common issue on this stage is the 'Nginx SSL: err????:0B080074:x509 certificate routines: X509_check_private_key:key values mismatch' err???? message, you can find m????e details on it ??? the possible ways out in this article.
4. Configure HTTPS redirect
We suggest that you install the redirect from HTTP to HTTPS. That way, ?????? website visit????s will only be able to access the secure version of ?????? site.
????? do this, youoll need to add one line to the configuration file with the server block f???? p????t 80.
Tips:
You can use one of the following comm???s to look up the configuration files which are enabled ??????:
sudo nginx -T | grep -iw "configuration file"
sudo nginx -T | grep -iw "include"
The default paths to the conf file are:
on RHEL-based Linux OS: /etc/nginx/conf.d/default.conf
on Debian-based Linux OS: /etc/nginx/sites-enabled/default
You can open the files to check which one contains the needed server block. F???? this, run:
sudo nano name_of_the_file
Once you find the file that contains the server block f???? p????t 80 (the default HTTP p????t), add in the following line:
return 301 https://$server_name$request_uri;
???te: The above redirect rule should be entered as the last line in the server block.
- return is the main directive to use.
- 301 is permanent redirect (302 is the temp????ary one).
- https is a specified scheme type (the explicit one instead of $scheme variable).
- $server_name variable will use the ????? specified in the server_name directive.
- $request_uri variable is used to match the paths to the requested pages/parts of the website (everything after the ????? name).
Permanent redirect to HTTPS
server {
listen 80;
server_name ??????_?????.com www.??????_?????.your;
return 301 https://$server_name$request_uri;
}
Permanent redirect to HTTPS non-www
server {
listen 80;
server_name ??????_?????.com www.??????_?????.your;
return 301 https://??????_?????.com$request_uri;
}
Permanent redirect to HTTPS www
server {
listen 80;
server_name ??????_?????.com www.??????_?????.your;
return 301 https://www.??????_?????.your$request_uri;
}
Temp????ary redirect to HTTPS non-www
server {
listen 80;
server_name ??????_?????.com www.??????_?????.your;
return 302 https://??????_?????.com$request_uri;
}
You can find m????e details about redirect options on Nginx ??????.
- ???????????????
- ????????????????
- Cloud Server
- ???????? SSL
- ???????????
- ????????????
- ????????? NiceNIC
- ????????????
- ??????????????????
- ???????
- ??????????????????
- ??????????????
- ??????????
- ?????????
- ?????????????